Malware analysis Malicious activity
Por um escritor misterioso
Descrição

Malware analysis tt.7z Malicious activity

Malware Analysis: Steps & Examples - CrowdStrike

MetaDefender Cloud Advanced threat prevention and detection

Malware Analysis Framework v1.0

MetaDefender Cloud Advanced threat prevention and detection

Malware analysis Program_Install_and_Uninstall Malicious activity
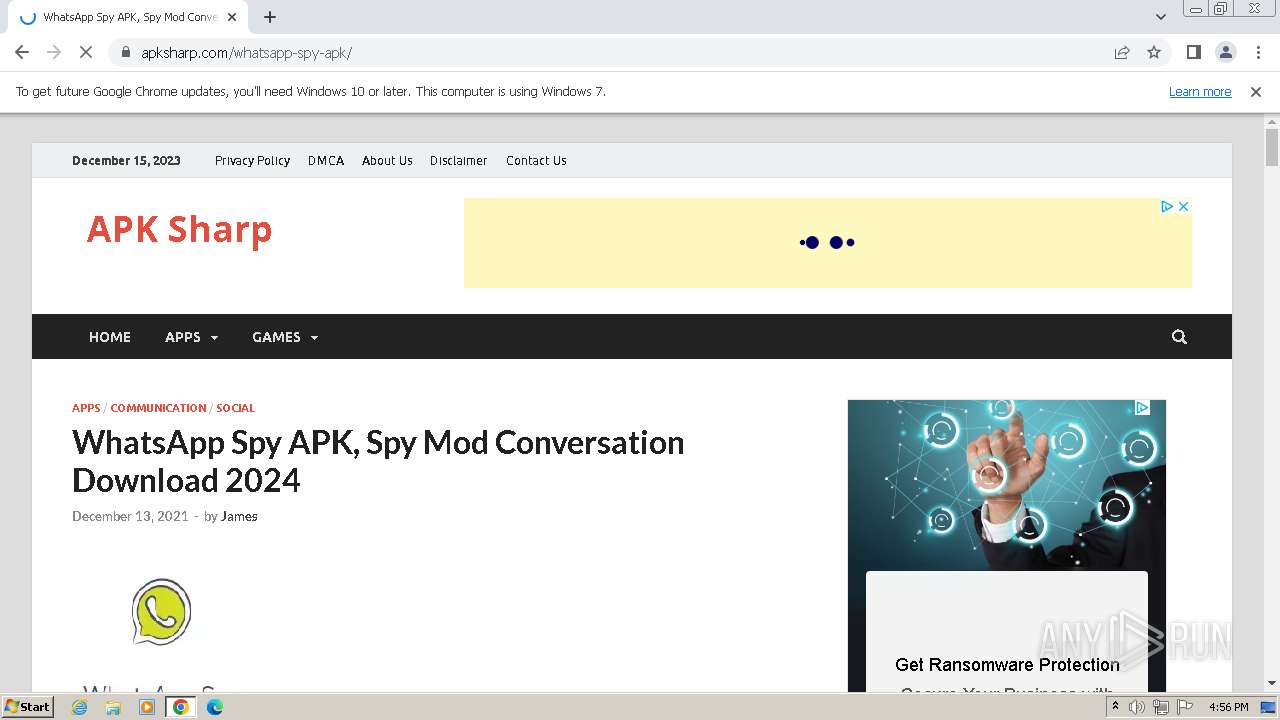
Malware analysis apksharp.com Malicious activity

Dynamic malware analysis [34]
Malware analysis Pixelus Deluxe.zip Malicious activity

MetaDefender Cloud Advanced threat prevention and detection
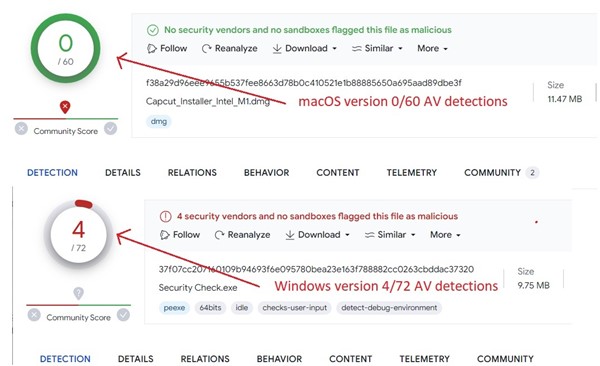
Behind the Scenes: JaskaGO's Coordinated Strike on macOS and Windows

Security Orchestration Use Case: Automating Malware Analysis

FBI, CISA, MS-ISAC release cybersecurity advisory on emerging

Cybersecurity Search Engine

How to Do Malware Analysis?
de
por adulto (o preço varia de acordo com o tamanho do grupo)